List of Top 15 Most Dangerous Hacker In The World, Hakers are around since the dawn of computers, or we can say they are the most dangerous people in the world and they’ve wreaked additional havoc than many people notice.
law enforcement has yet to catch up with several of their antics. Here is a roundup of the most well-known hackers and what they’ve become infamous for within the hacker community.
Hackers are the ones who are just not the hackers they are billionaires they are the ones who stole the information from one country to another. They are a useful weapon for any country but also dangerous if they are been hack too. Today we will discuss the world’s most dangerous hackers of all time.
The ever-changing technological world has made hackers a serious concern for governments, companies, and people. Infiltrating and manipulating computer systems to cause disruption and destruction is within the capabilities of these talented people.
There is a growing threat from hackers due to the ever-expanding digital ecosystem. Here we’ll take a look at the top 10 most dangerous hackers of 2024, dissecting their histories, techniques, and the harm they’ve done.
Any number of people, from infamous criminal masterminds to nameless hacktivists, may cause massive chaos and devastation if given the chance. Get ready to hear the stories of the future’s most notorious and terrifying hackers.
Top 15 Most Dangerous Hackers in World 2024
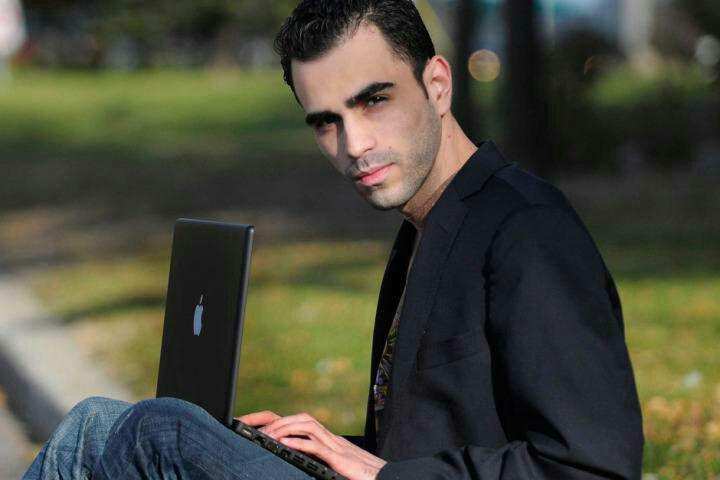
15. Marc Rogers

Source: Twitter / @marcwrogers
Marc Rodgers, a cybersecurity specialist and ethical hacker, has worked in the field since the 1980s.
Throughout his twenty-year hacking career, he has successfully compromised several well-known systems and gadgets, such as Apple’s TouchID and the Tesla Model S, thereby improving the security of these systems for both parties.
On the BBC series “The Real Hustle,” one of Rodgers’ most recognizable television roles is that of an on-screen specialist in technological frauds.
He has also provided technical assistance for the USA Network drama “Mr. Robot” and helped design hacks for the show.
Both his work with the US Ransomware Taskforce and his founding of DEF CON, the biggest hacking convention in the world, have brought Rodgers a global following in recent years.
Additionally, he is the driving force behind the CTI League, an alliance of experts, government entities, and law enforcement that collaborates to safeguard healthcare businesses and other vital sectors from cyber threats.
https://www.youtube.com/watch?v=CQMQVrTeq7A&pp=ygULTWFyYyBSb2dlcnM%31
14. Charlie Miler:

Source: Youtube
Dr. Charlie Miller, a former NSA hacker and the first person to hack an iPhone and an Android phone became famous throughout the world when he and his research colleague Chris Valasek acquired remote control of a 2014 Jeep Cherokee from almost ten miles away.
He is well-known for discovering security flaws in many Apple devices, including the iPhone, MacBook Air, and the App Store. As a result, Apple rethought its approach to security.
As a result, Dr. Miller found himself featured on several media sites and asked to speak at security conferences and events worldwide. This captured the attention of the security community.
Among security professionals, Dr. Miller is now widely considered to be among the top hackers on the planet.
Earlier this year, he became a member of the SANS Institute, where he instructs students from all around the globe in ethical hacking and security research. His work has cemented his status as a legendary hacker in the annals of cybersecurity.
https://www.youtube.com/watch?v=_Tciqg2baOw&pp=ygUOQ2hhcmxpZSBNaWxlcjo%3D
13. HD- Moore

Source: Youtube
Hi-Def Moore Moore’s development of the vulnerability scanning program Metasploit has revolutionized hacking and earned him international recognition. Moore started working on the Metasploit Project in the early 2000s.
It’s a program that security researchers and testers use to hunt for vulnerabilities in computers. Metasploit is now a leading testing framework that powers many of the best pen testing tools available.
Security professionals now have a robust and standardized toolbox at their disposal, which greatly simplifies the process of finding and exploiting vulnerabilities.
Moore is an authority in several fields, including Metasploit, network security, vulnerability research, and incident response. Moore is an outspoken supporter of security education and awareness campaigns.
Working on the Metasploit Project and giving speeches have helped him spread the word about the dangers of cybercrime, which he thinks everyone should be aware of.
Moore, widely regarded as one of today’s top hackers, also serves as Chairman and Founding Chief Technology Officer of runZero.
https://www.youtube.com/watch?v=11y1TcQwCM8&pp=ygUJSEQtIE1vb3Jl
12. Linus Torvalds

source: Aalto University/YouTube
Linus Torvalds is one of the most well-known hackers on Earth for developing the Linux kernel, the system software that powers Linux. Linux soon became an OS with much more power and flexibility than its predecessor.
Torvalds made the Linux kernel available under the GNU General Public License, granting everyone the freedom to use, alter, and distribute it. Hackers and computer aficionados took to the Linux kernel like flies.
Linux now has millions of users around the globe. Supercomputers, embedded devices, and servers often use it as their operating system of choice.
On mobile devices, Linux is also finding more and more applications. The collaborative nature of Linux, which Torvalds was an early proponent of, highlights the strength of dispersed cooperation and the aggregate knowledge of the worldwide development community.
It has influenced the trajectory of open-source software. All it took was a small exploit on an old OS.
https://www.youtube.com/watch?v=S5S9LIT-hdc&pp=ygUOTGludXMgVG9ydmFsZHM%3D
11 .Greg Hoglund

Source: Wikispooks.com
Hackers may use buffer overflows, a type of software vulnerability, to gain unauthorized access to computer systems. Greg Hoglund was among the first to study and write about them.
He started the security consulting company HBGary in the late ’90s; they focus on incident response and testing. Fortune 500 corporations, government agencies, and law enforcement organizations are among the clients that HBGary has worked with.
A dispute involving the hacktivist organization Anonymous engulfed HBGary in 2011. The whole thing started when Aaron Barr, CEO of HBGary, said he had found important Anonymous members and planned to expose their names.
As a result, Anonymous struck back against HBGary Federal’s infrastructure. After breaking into the company’s systems, the hackers made off with sensitive papers, emails, and more. Hoglund was accused of helping the FBI understand Anonymous, but he refuted the claims and said that all he was doing was attempting to infiltrate Anonymous.
This incident altered the course of ethical hacking for the better by casting doubt on the nature of the partnership between security researchers and police departments.
https://www.youtube.com/watch?v=34-UCGc6SfE&pp=ygUMR3JlZyBIb2dsdW5k
10. Loyd Blankenship

Source: ffccsd.org
Written under the hacker identity “The Mentor,” Loyd Blankenship’s most renowned work is the Hacker Manifesto.
Hackers often look to the manifesto as a source of motivation and a defense of lawful hacking; it posits that hackers are more akin to explorers and innovators than criminals.
Blankenship said that hacking may assist in building defenses against assaults, making it a useful weapon for social change. The publication of the Hacker Manifesto, however, did not silence its critics.
While some see it as an important expression of hacker ideology, others think it encourages criminal behavior.
Blankenship has done more than just write a manifesto. Being a part of the notorious hacker ring Legion of Doom, he helped pave the way for contemporary cybersecurity measures.
His early engagement with the hacking community had a significant impact on its developing culture and ethics.
https://www.youtube.com/watch?v=0tEnnvZbYek&pp=ygUUMTUuIExveWQgQmxhbmtlbnNoaXA%3D
9. Abene Mark

Source: mejoreshackerfamosos
Abene, better known by his hacker moniker “Phiber Optik,” is widely considered to be among the most infamous individuals in the history of phone hacking.
Abene first gained notoriety as an associate of the highly skilled hacker gang Masters of Deception (MoD), which was responsible for several high-profile breaches in the world of telecommunications.
They accomplished a lot, one of which was delving into the mysterious realm of phone phreaking, the practice of modifying phone networks for the sake of curiosity rather than harm.
However, the MoD charged Abene and four other members with conspiracy to commit computer fraud in July 1992. They had accessed the systems of several businesses, including AT&T, Bank of America, and the National Security Agency (NSA).
It was the opinion of many, both inside and outside the hacking community, that Abene was unfairly convicted and used as an example.
After his release from probation, Abene began working as a security consultant. Among his many employers were the New York City Police Department and IBM.
In addition, he established Security Metrics, his own security consulting business. In the security industry, Abene has become a revered figure. His ability to explain complex security concepts in simple terms has made him well-known in the field of computer security.
https://www.youtube.com/watch?v=7c-LqjuvFT4&pp=ygUKQWJlbmUgTWFyaw%3D%3D
8. Shimomura Tsutomu

Source: Youtube
While still a black-hat hacker, Kevin Mitnick decided to get into cybersecurity specialist Tsutomu Shimonura’s computer in 1995. Mitnick was, needless to say, not pleased with the outcome.
After Mitnick evaded capture for a while, Shimomura was determined to exact his vengeance by assisting the FBI in locating and apprehending him.
This partnership was a watershed moment in the evolution of ethical hacking; it brought attention to the idea of hackers assisting law enforcement.
Shimomura’s reputation as one of the world’s top hackers extends beyond his role in Mitnick’s demise.
He was in high demand as a consultant, lecturer, and educator due to his extensive knowledge in cryptography, system design, and network security.
Additionally, he stresses the significance of ethical hacking practices and the value of applying one’s expertise for the benefit of society.
His legacy rests on this moral compass, which encourages would-be hackers to do good deeds with their skills rather than evil ones.
https://www.youtube.com/watch?v=EsmsakXuae8&pp=ygURU2hpbW9tdXJhIFRzdXRvbXU%3D
7 T. Morris

Source: technocrazed.com
The first Morris worm, a sort of malware that could propagate via the Internet and gather data on computers, was built by Robert Tappen Morris in 1988, when he was still a Harvard student.
Damage to computer systems was extensive as the Morris worm rapidly multiplied, causing extensive damage to computer systems.
The virus almost brought down NASA’s systems and infected an estimated 6,000 computers throughout the United States, including those used for military research.
The new Computer Fraud and Abuse Act of 1986 arrested Morris, found him guilty, and sentenced him to three years of probation, 400 hours of community service, and a $10,000 fine.
In the realm of cybersecurity, Morris has emerged as a divisive figure. Many think Morris’s primary intention was to infect school computers with his software, making them seem sluggish and forcing the school to patch or upgrade them.
His friends and acquaintances said he made it just to test the internet’s boundaries and how far his worm could go. Indeed, Morris became one of the most renowned and accomplished hackers on the planet when the Morris worm served as a wake-up call to the security industry.
According to some experts, the security business as we know it today may have sprung from the worm.
https://youtu.be/SKi2qE9xK1c?si=AjhsJTJg2nsY-rZ3
6. Michael CALCE
In February 2000, 15-year-old Michael Calce also called “Mafia boy” discovered the way to take over networks of university computers and used their combined resources to disrupt the number-one search engine at the time: Yahoo.
within a week, he’d also brought down the dell, eBay, CNN, and Amazon employing a dedicated denial of service (DDoS) attack that weak company servers and caused websites to crash.
Calce’s warning sign was maybe the foremost jarring for investors and net proponents. If the most important web site within the world — valued at over $1 billion — might be so simply sidelined, was any online data actually safe? it is not an exaggeration to say that the event of law-breaking legislation suddenly became a high government priority due to Calce’s hack.
https://youtu.be/q0pKpqebwMI?si=xOcinkmfOuUYmv8r
5 GUCCIFER 2.0

Guccifer 2.0 is a person or organization which can break into the DNC, the National Democratic Committee. Which had information coded and which they leaked to Wikileak? This material was read by the press.
This high profile prosecution was taken up by the US government. The intelligence community has been faced with many challenges and cyber attacks have been undertaken.
This group could also have intervened with the presidential election in the USA in 2016, but those allegations were not proven, although President Donald Trump claimed the election was being exploited. And it’s Russian intelligence that people are behind it, but he won the election, so he’s worried about it.
https://www.youtube.com/watch?v=XLAaS7VKT1g&pp=ygUMR3VjY2lmZXIgMi4w
4. LIZARD SQUAD
DDoS attacks are known. It’s a dangerous way of attacking. Such attacks lead to manipulation and hackers may interrupt the infrastructure to obtain access to personal information from people.
One of their first major attacks was known to shut down a lizard League of Legends servers. Other titles have been shut down like Destiny. The PlayStation networks and Xbox were shut down live by an intruder.
https://worldstopinsider.com/worlds-top-10-fastest-cars-of-all-time/
There were major fake warnings by a lizard. The FBI was involved and fortunately, the charges were unfounded. Twitter, Snapchat and Tinder were also hacked.
We said that a bomb was inserted into Sony’s flight, on which the president was at the helm. John Smedley thought he was gone.
https://www.youtube.com/watch?v=97xw3OyMKEU&pp=ygUMTGl6YXJkIHNxdWFk
3. ENSON JAMES ANCHETA

Jeanson James Ancheta did not have an interest in credit card data hacking schemes or collapsing social justice networks.
Rather, Ancheta was concerned about the use of bots — software-based robots that manipulate computer systems and ultimately control them. In 2005, he was able to compromise over 400,000 computers using a series of large-capacity botnets.
He was then lent to advertising firms, according to Ars Technica, and also charged to load bottoms or adware directly on certain computers. A 57-month prison sentence was awarded to Ancheta and the first time a botnet technology hacker was sent to prison.
https://www.youtube.com/watch?v=CEWwNeuH8UY&pp=ygUdamVhbnNvbiBqYW1lcyBhbmNoZXRhIGhhY2tlciA%3D
2. JONATHAN JAMES
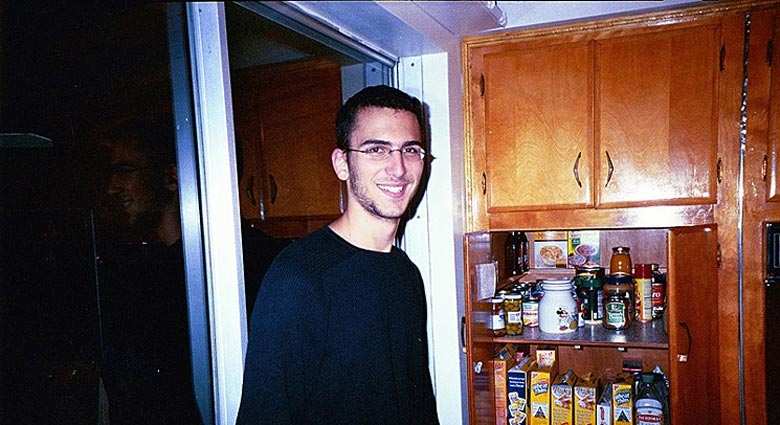
Jonathan James hacked into numerous businesses with the alias cOmrade. The New York Times said however that his hack into the United States Department of Defense’s computers was what really won him recognition.
The most shocking was that James was only fifteen at the moment. James was charged in 2000, sentenced to six months of house arrest, and forbidden from using software for fun. Nevertheless, he was sent to six months in jail for a probation violation.
Jonathan James was accused of violations of the rules on cybercrime as the youngest person. In 2007, TJX was hacked, a department store, which affected its consumers.
In spite of the lack of evidence, investigators believed James could be involved. In 2008, Johnathan James finally shot himself.
https://www.youtube.com/watch?v=IVZOXKm2ML0&pp=ygUOSm9uYXRoYW4gSmFtZXM%3D
1. KEVIN POULSEN

Sometimes in their daily lives, hackers may seem perfectly harmless. Take the famous and legal website, Kevin Poulsen, now wired.com editor for the news.
Nevertheless, he was once a black-hats programmer who was doing such tricks that by hacking their telephone lines he was the 102nd recipient, earning a Porschen 944 S2 from KIIS-FM.
Like other hackers, by finding MySpace users who were searching for child porn, he used his resources for the greater good. Nevertheless, he also picked up FBI machines and eventually completed a five-year term.
https://worldstopinsider.com/beautiful-teenage-actress/
He has since written, not just wired but his novel Kingpin has concentrated on his writing career.
Some of these top hackers aimed to form the world an improved place, others to prove UFO theories. Some wished cash and a few hoped for fame, however, all played a critical role in the evolution of cybersecurity.
Hacker is a person who uses computers to induce illegal access to data. Hacking isn’t against the law unless and until you are doing it for illegal activities.
Stealing data and hacking into networks don’t seem to be the only things that hacker does, So you want to be hack then you should because nowadays everything is based online and there is a lot of job being an offer by the government.
https://www.youtube.com/watch?v=8s4b2ZKyPHc&pp=ygUPwqBLRVZJTiBQT1VMU0VO
Conclusion
In order to successfully fight cybercrime, some of these hackers have worked closely with authorities, sharing their information and skills.
Other malevolent hackers have been apprehended and possible cyber threats have been averted because to this collaboration. Highlighting the achievements and valuable contributions of these elite hackers, the essay emphasizes the pressing need for strong cybersecurity measures in the modern digital world.
That hacker, with their sophisticated methods and dogged search for security holes, are still very much a concern is something this incident serves to remind us of.
Individuals, businesses, and governments must always be on the lookout for threats to their digital assets in order to keep up with the rapid pace of technological change.
Top 10 Lists of the people, things, places, most expensive, animals, most popular, luxury and high rankings of world. World's Top Insider focuses on the top ten lists of best, greatest and top rankings in the world.



